L’évolution de la fintech et de réglementation au Maroc et en Afrique
Contents
Évolution de la fintech au Maroc et en Afrique. 6
Les principaux facteurs de croissance. 6
Les défis du secteur fintech. 7
Évolution de la réglementation de la fintech au Maroc et en Afrique. 7
2.1 Croissance de la Fintech. 10
2.2 Acteurs clés du secteur. 10
2.3 Réglementation en vigueur. 11
III. Réglementation de la Fintech au Maroc. 11
3.2 Initiatives de régulation. 12
3.3 Impact sur l'industrie. 12
4.1 Révolution Fintech dans divers pays africains. 13
4.2 Solutions de paiement novatrices. 13
4.3 Utilisation des services financiers mobiles. 13
6.1 Récapitulatif des points clés. 14
6.2 Perspectives pour l'avenir. 14
I. Introduction
1.1 Contexte de la Fintech
La Fintech est un secteur en pleine évolution au Maroc et en Afrique. Bien que le Maroc accuse un certain retard par rapport à d'autres pays africains, le pays commence à innover et à devenir un centre de technologie financière en phase de démarrage[2]. Le Maroc dispose d'un important secteur bancaire qui peut être consacré au développement de ce secteur technologique[2]. En outre, la réglementation marocaine ne pose pas de freins particuliers au développement des fintech[1][2][3][5].
1.2 Objectifs de l'article
Cet article vise à examiner l'évolution de la Fintech et de la réglementation au Maroc et en Afrique. Les sources d'information dans l'article sont les suivantes:
- [1] Finances News Hebdo: Cet article souligne que le secteur de la Fintech accuse un net retard par rapport à d'autres pays africains. Il met également en évidence le potentiel des fintech au Maroc et les défis à relever pour leur développement.
- [2] Industries.ma: Cet article indique que le paysage de la Fintech au Maroc est en pleine évolution et que le Maroc commence à devenir un centre de technologie financière en phase de démarrage. Il souligne également les avantages concurrentiels que les start-up de la Fintech au Maroc peuvent offrir par rapport aux banques traditionnelles.
- [3] Laquotidienne.ma: Cet article examine les défis et les opportunités liés à l'utilisation de l'intelligence artificielle dans le secteur de la Fintech au Maroc. Il met également en évidence la croissance rapide du marché de la Fintech au Maroc et les avantages concurrentiels des start-up de la Fintech.
- [4] Challenge.ma: Cet article souligne que le Maroc est encore à la traîne en matière de Fintech, mais qu'il dispose d'une réelle opportunité de faire du Maroc un centre de technologie financière. Il met également en évidence les initiatives lancées par les autorités publiques pour promouvoir la Fintech.
- [5] PwC Maroc: Cet article examine les Fintech en Afrique et souligne que le Maroc dispose d'un écosystème Fintech encore embryonnaire mais en évolution. Il met également en évidence les avantages non négligeables dont dispose l'Afrique pour combler l'écart avec les autres régions du monde.
- [6] Finances News Hebdo: Cet article examine la place de la Fintech dans l'écosystème entrepreneurial et des start-up au Maroc. Il met également en évidence le potentiel des fintech au Maroc et les défis à relever pour leur développement.
En somme, les sources d'information examinées dans cet article soulignent que le Maroc dispose d'un important potentiel pour le développement de la Fintech, mais qu'il doit relever certains défis pour y parvenir. La réglementation marocaine ne pose pas de freins particuliers au développement des fintech, mais elle est encore en évolution[3][5]. Les start-up de la Fintech peuvent offrir plusieurs avantages concurrentiels par rapport aux banques traditionnelles[2][3]. Les autorités publiques ont lancé des initiatives pour promouvoir la Fintech[4][6].
Citations:
[1] https://fnh.ma/article/actualite-financiere-maroc/fintech-au-maroc-l-ecosysteme-peine-a-decoller
[2] https://industries.ma/fintech-le-maroc-simpose/
[3] https://laquotidienne.ma/article/economie/fintech-intelligence-artificielle-technologie
[4] https://www.challenge.ma/fintechs-le-maroc-encore-a-la-traine-249734/
[5] https://pwcmaroc.pwc.fr/fr/publications-communique-de-presse/fintechs-en-afrique.html
II. Évolution de la Fintech au Maroc
2.1 Croissance de la Fintech
Le marché de la Fintech au Maroc est en croissance rapide[1][2]. Selon un rapport publié par le cabinet de conseil en stratégie Boston Consulting Group (BCG) en 2019, le Maroc comptait environ 80 start-up de la Fintech en 2018, soit une croissance de 60% par rapport à l'année précédente[1]. Les domaines de la Fintech les plus actifs au Maroc étaient les paiements en ligne, les transferts d'argent et la finance participative[1]. Le Maroc dispose d'un important potentiel de croissance pour la Fintech en raison de sa population jeune et connectée, de l'augmentation de l'accès à Internet et des smartphones, ainsi que de la volonté du gouvernement marocain de promouvoir l'innovation technologique dans le secteur financier[1][2][3].
2.2 Acteurs clés du secteur
Le paysage de la Fintech au Maroc est en pleine évolution et le Maroc commence à devenir un centre de technologie financière en phase de démarrage[2][3]. Le Maroc compte environ 80 start-up de la Fintech[1]. Les acteurs clés du secteur sont les start-up de la Fintech, les banques traditionnelles et les autorités publiques[2][3]. Les start-up de la Fintech peuvent offrir plusieurs avantages concurrentiels par rapport aux banques traditionnelles, notamment l'innovation[1][2]. Les banques traditionnelles peuvent jouer un rôle important dans le développement de l'écosystème des Fintech en partageant leur expertise, leur savoir-faire, leurs données clients ainsi que leurs agréments avec des start-up porteuses de projets innovants[2].
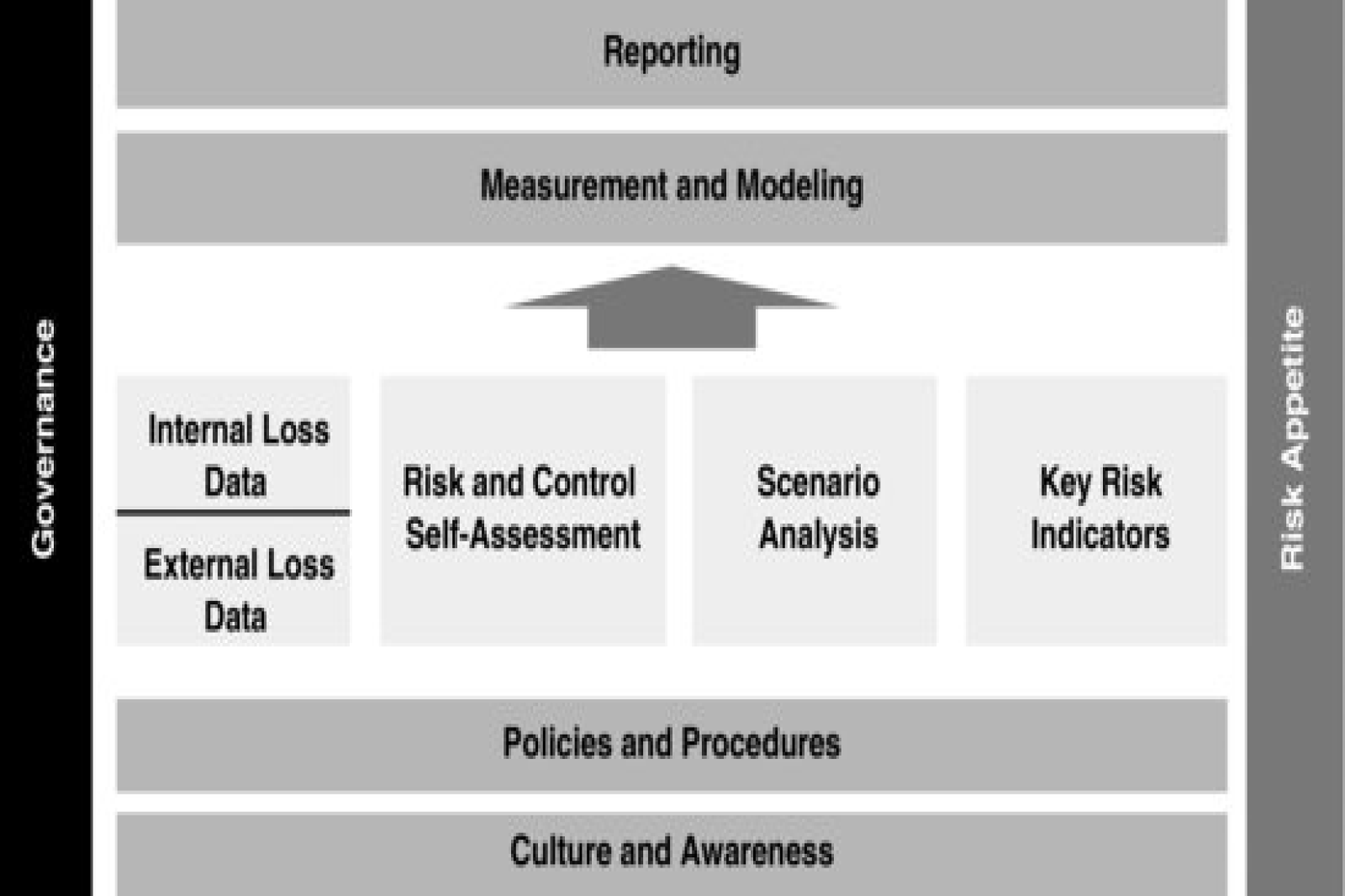
2.3 Réglementation en vigueur
La réglementation marocaine en matière de Fintech est encore en évolution[1][2]. Les start-up de la Fintech doivent obtenir des autorisations et des licences de la Banque centrale et de l'Autorité marocaine du marché des capitaux (AMMC) pour offrir certains produits et services financiers[1]. Toutefois, la réglementation marocaine ne pose pas de freins particuliers au développement des Fintech[1][2][3][4]. La réglementation marocaine fait adhérer l'ensemble des utilisateurs à un système de confiance grâce à Bank Al-Maghrib[4]. Toutefois, la place gagnerait à formaliser un cadre règlementaire pour l'open banking[2].
En somme, le marché de la Fintech au Maroc est en croissance rapide et le pays commence à devenir un centre de technologie financière en phase de démarrage[1][2][3]. Les acteurs clés du secteur sont les start-up de la Fintech, les banques traditionnelles et les autorités publiques[2][3]. La réglementation marocaine en matière de Fintech est encore en évolution, mais elle ne pose pas de freins particuliers au développement des Fintech[1][2][3][4]. Les start-up de la Fintech peuvent offrir plusieurs avantages concurrentiels par rapport aux banques traditionnelles[1][2].
Citations:
[1] https://laquotidienne.ma/article/economie/fintech-intelligence-artificielle-technologie
[2] https://fnh.ma/article/actualite-financiere-maroc/fintech-au-maroc-l-ecosysteme-peine-a-decoller
[3] https://industries.ma/fintech-le-maroc-simpose/
[4] https://pwcmaroc.pwc.fr/fr/publications-communique-de-presse/fintechs-en-afrique.html
[5] https://www.challenge.ma/fintechs-le-maroc-encore-a-la-traine-249734/
[6] https://fnh.ma/article/actualite-financiere-maroc/economie-numerique-le-potentiel-des-fintech-au-maroc-pas-encore-pleinement-exploite
III. Réglementation de la Fintech au Maroc
3.1 Cadres réglementaires
La réglementation marocaine en matière de fintech est encore en évolution[1][2][3][4][5]. Les start-up de la fintech doivent obtenir des autorisations et des licences de la Banque centrale et de l'Autorité marocaine du marché des capitaux (AMMC) pour offrir certains produits et services financiers[1][3]. Toutefois, la législation marocaine n'interdit ni n'entrave la création de sociétés de technologie financière, car il n'existe pas de réglementation spécifique à l'heure actuelle[2][4][5]. La réglementation marocaine ne pose pas de freins particuliers au développement des fintech[1][2][3][4][5]. Toutefois, la place gagnerait à formaliser un cadre règlementaire pour l'open banking[2][3].
3.2 Initiatives de régulation
Les autorités publiques ont lancé des initiatives pour promouvoir la fintech au Maroc[1][4][5]. La Banque centrale du Maroc encourage le système financier bien structuré du pays à investir dans l'adoption du numérique[2]. En 2018, la Banque Populaire a lancé la première édition du programme Fintech Challenge et Open Innovation pour montrer les opportunités dans ce secteur à niveau continental, notamment pour les start-up africaines par le biais de partenariats et de financements[4]. Toutefois, le développement de la fintech au Maroc nécessite une révision de fond de la licence bancaire et des établissements de crédits[1][5].
3.3 Impact sur l'industrie
La réglementation marocaine en matière de fintech a un impact sur l'industrie[1][3]. La réglementation complexe et incertaine peut rendre difficile pour les start-up de naviguer dans cet environnement[1][3]. Toutefois, la réglementation marocaine ne pose pas de freins particuliers au développement des fintech[1][2][3][4][5]. Les start-up de la fintech peuvent offrir plusieurs avantages concurrentiels par rapport aux banques traditionnelles[1][2][3]. Le développement de l'écosystème des fintech au Maroc demeure tributaire de la volonté des banques à partager leur expertise, leur savoir-faire, leurs données clients ainsi que leurs agréments avec des start-up porteuses de projets innovants[2]. En somme, la réglementation de la fintech au Maroc est encore en évolution, mais elle ne pose pas de freins particuliers au développement des fintech[1][2][3][4][5].
Citations:
[1] https://fnh.ma/article/actualite-financiere-maroc/fintech-au-maroc-l-ecosysteme-peine-a-decoller
[2] https://www.lopinion.ma/Economie-numerique-La-reglementation-de-la-fintech-demeure-limitee-au-Maroc_a31202.html
[3] https://laquotidienne.ma/article/economie/fintech-intelligence-artificielle-technologie
[4] https://industries.ma/fintech-le-maroc-simpose/
[5] https://fnh.ma/article/actualite-financiere-maroc/economie-numerique-le-potentiel-des-fintech-au-maroc-pas-encore-pleinement-exploite
[6] https://www.challenge.ma/fintechs-le-maroc-encore-a-la-traine-249734/
IV. Expansion de la Fintech en Afrique
4.1 Révolution Fintech dans divers pays africains
La Fintech est en pleine expansion en Afrique, avec une croissance rapide dans de nombreux pays[2][3][4][5]. Selon un rapport de McKinsey, les revenus cumulés des sociétés de Fintech en Afrique pourraient être multipliés par huit d'ici à 2025, pour atteindre 30 milliards de dollars[2]. Les pays africains les plus actifs dans le domaine de la Fintech sont le Nigeria, l'Afrique du Sud, le Kenya, le Ghana et l'Egypte[2][3][4]. Les Fintech africaines ont de beaux jours devant elles, car elles offrent des solutions innovantes pour répondre aux besoins financiers des populations africaines[2][3][4][5]. Les investissements dans la Fintech en Afrique ont augmenté de manière significative ces dernières années, passant de 400 millions de dollars en 2017 à plus de 2 milliards de dollars en 2021[5].
4.2 Solutions de paiement novatrices
Les Fintech africaines ont développé des solutions de paiement novatrices pour répondre aux besoins des populations africaines[2][3][4][5]. Les solutions de paiement mobile, telles que M-Pesa au Kenya, ont révolutionné le secteur des paiements en Afrique[2][3][4][5]. Les Fintech africaines ont également développé des solutions de paiement en ligne, des portefeuilles électroniques et des plateformes de transfert d'argent[2][3][4][5]. Ces solutions ont permis de réduire les coûts de transaction et d'améliorer l'inclusion financière en Afrique[2][3][4][5].
4.3 Utilisation des services financiers mobiles
Les services financiers mobiles sont de plus en plus utilisés en Afrique[2][3][4][5]. Les Fintech africaines ont développé des solutions de paiement mobile pour répondre aux besoins des populations africaines, qui ont souvent un accès limité aux services bancaires traditionnels[2][3][4][5]. Les services financiers mobiles permettent aux utilisateurs de transférer de l'argent, de payer des factures et d'effectuer des transactions financières à partir de leur téléphone portable[2][3][4][5]. Les services financiers mobiles ont permis d'améliorer l'inclusion financière en Afrique, en permettant à des millions de personnes d'accéder à des services financiers de base[2][3][4][5].
En somme, la Fintech est en pleine expansion en Afrique, avec une croissance rapide dans de nombreux pays[2][3][4][5]. Les Fintech africaines ont développé des solutions de paiement novatrices pour répondre aux besoins des populations africaines, en utilisant notamment les services financiers mobiles[2][3][4][5]. Les investissements dans la Fintech en Afrique ont augmenté de manière significative ces dernières années, passant de 400 millions de dollars en 2017 à plus de 2 milliards de dollars en 2021[5].
Citations:
[1] https://www.africafintechnetwork.com
[2] https://www.lemonde.fr/economie/article/2023/05/03/en-afrique-le-decollage-des-fintech_6171865_3234.html
[3] https://www.mckinsey.com/~/media/mckinsey/industries/financial%20services/our%20insights/fintech%20in%20africa%20the%20end%20of%20the%20beginning/fintech-in-africa-the-end-of-the-beginning.pdf
[4] https://www.mckinsey.com/industries/financial-services/our-insights/fintech-in-africa-the-end-of-the-beginning
[5] https://www.un.org/africarenewal/magazine/august-2022/fintech-other-knowledge-intensive-services-could-drive-africa%E2%80%99s-prosperity
[6] https://industries.ma/fintech-le-maroc-simpose/
VI. Conclusion
6.1 Récapitulatif des points clés
La Fintech est en pleine évolution au Maroc et en Afrique, avec une croissance rapide dans de nombreux pays[1][2][3][4][5]. Le Maroc commence à devenir un centre de technologie financière en phase de démarrage, avec environ 80 start-up de la Fintech en 2018[1][2]. Les acteurs clés du secteur sont les start-up de la Fintech, les banques traditionnelles et les autorités publiques[1][2][3][5]. La réglementation marocaine en matière de Fintech est encore en évolution, mais elle ne pose pas de freins particuliers au développement des Fintech[1][2][3][4][5]. Les besoins en matière de régulation de la Fintech en Afrique sont nombreux, notamment en matière d'harmonisation des réglementations nationales et de protection des consommateurs[1][2][5].
6.2 Perspectives pour l'avenir
L'avenir de la Fintech au Maroc et en Afrique est prometteur, avec un fort potentiel de croissance[1][2][3][4][5]. Les Fintech africaines ont développé des solutions de paiement novatrices pour répondre aux besoins des populations africaines, en utilisant notamment les services financiers mobiles[2][3][4][5]. Les investissements dans la Fintech en Afrique ont augmenté de manière significative ces dernières années, passant de 400 millions de dollars en 2017 à plus de 2 milliards de dollars en 2021[5]. Toutefois, les défis réglementaires en Afrique sont nombreux, notamment en raison de la diversité des réglementations nationales et de l'absence de réglementation spécifique à la Fintech[5]. Les autorités publiques doivent mettre en place des réglementations claires et cohérentes pour encourager le développement de la Fintech[1][2][5]. Les réglementations doivent être adaptées aux besoins des start-up de la Fintech et favoriser l'innovation[2][5]. Les réglementations doivent également protéger les consommateurs et garantir la stabilité financière[2][5].
En somme, la Fintech est un secteur en pleine évolution au Maroc et en Afrique, avec un fort potentiel de croissance et des défis réglementaires à relever[1][2][3][4][5]. Les autorités publiques doivent travailler en étroite collaboration avec les start-up de la Fintech pour comprendre les défis auxquels elles sont confrontées et élaborer des réglementations adaptées[2][5]. L'avenir de la Fintech en Afrique est prometteur, avec des solutions novatrices pour répondre aux besoins des populations africaines et des investissements en hausse[2][3][4][5].
Citations:
[1] https://www.umgc.edu/current-students/learning-resources/writing-center/writing-resources/writing/essay-conclusions
[2] https://writingcenter.unc.edu/tips-and-tools/conclusions/
[3] https://www.grammarly.com/blog/how-to-write-a-conclusion/
[4] https://owl.purdue.edu/owl/general_writing/common_writing_assignments/argument_papers/conclusions.html
[5] https://www.indeed.com/career-advice/career-development/how-to-write-a-conclusion
[6] https://www.masterclass.com/articles/how-to-write-a-conclusion



POST COMMENT
COMMENTS(0)
No Comment yet. Be the first :)